A computer virus or malware is meant to spy on you and steal your valuable data or simply use your system resources. Causing your hardware to break and making your PC unusable is not in a hacker’s best interest.
However, there will be instances when a computer virus can damage the hardware. Sometimes, it’s actual physical damage that occurs as a result of overuse. Other times, it’s just such a nasty malware that you can’t get rid of it no matter what you do. So, even when your hardware isn’t technically broken, it is still useless. Since you can’t clear the infection, you’ll want to replace it.
I dug a little deeper and found not one or two but nine different ways a computer virus can take a toll on various hardware components. Here they are!
1.Block/reset your PC with CPU overclocking
Overclocking is the action that leads to increasing the CPU’s clock rate. Its consequences include premature wear, additional heat release, increased need for extra cooling and maintenance. But most importantly, overclocking can lead to a CPU blockage, therefore a blockage or a restart of the PC.
What causes your CPU to overclock? It can happen because of:
- A user’s deliberate action to speed up the CPU;
- A worm, virus, or another type of malware infection consequence of maxing out the processor;
- A hacker’s direct attempt to tamper the CPU’s voltage settings in BIOS.
As you probably know, if your computer is running slower and freezes or crashes unexpectedly, it could be a sign of a virus infection. We’ve talked about it here.
Viruses and malware could consume your system resources and, among other things, max out your processor. A constantly overworked CPU will overheat, its thermal paste will dry out, and it will break much faster.

Power viruses go after your CPU
Some viruses could intentionally melt your CPU. We call them power viruses since they can run a particular code that will draw the most power from the processor, producing abnormal heat levels.
In older CPUs that lacked overheating protection, this was a severe issue. Power viruses would have exploited the fact that when a processor is in use, it resorts to specific electrical pathways in its microprocessor to act on particular instructions. By forcing the processor to work on the same instructions repeatedly, a power virus successfully overworked and broke the CPU.
Modern CPUs have some sort of protection
These days, however, CPUs incorporate modern technologies. Thanks to dynamic frequency and voltage scaling, plus the built-in thermal protection, it is less likely for the processor to be affected by such factors.
Modern CPUs with smart thermal protection can step in even if the hacker manages to tamper the CPU voltage settings in BIOS.
As soon as it senses that the processor is overworked, it will shut off to prevent it from breaking, even if the maximum voltage settings in BIOS haven’t been reached yet. How cool is that?
2.Fry your RAM
Some computer viruses or malware can fry your RAM through a recently discovered DRAM rowhammer hardware exploit.
Before we get into details, a few words on the RAM, in general, and DRAM operation, in particular.
What makes the DRAM so important and vulnerable
RAM stands for Random Access Memory, and every device, from PCs to game consoles, relies on it. Because it allows devices to access data at lightning speed, it represents one of the most critical components that dictate system performances.
There are two types of RAM: DRAM (Dynamic RAM) and SRAM (Static RAM).
DRAM is the type of RAM commonly used as the main memory of the device.
The hardware component that makes DRAM functional consists of millions of memory cells, all crammed inside a tiny chip. Each memory cell has an integrated circuit consisting of a transistor and a capacitor, with each capacitor storing a data bit.
This DRAM vulnerability seems to be specific to modern memory chips. The smaller and more compact they are made, the closer the memory cell rows will sit, and the higher the odds of tampering with them through the rowhammer method.

Enter DRAM rowhammer hardware exploit
So, the DRAM rowhammer hardware exploit is an attack on the memory cells. It was signaled by Google’s Project Zero team, who reported in 2015 that they could gain kernel privileges by exploiting the DRAM rowhammer bug.
The Project Zero team researchers discovered that, with some DRAM devices, if you repeatedly access a row of memory, bit flips will occur in the rows adjacent to the accessed row.
From 29 machines sold by different vendors – meaning they had different CPUs and DRAMs, 15 of them manifested a bit flip when repeatedly hammering their DRAM’s rows of memory cells.
How could hackers exploit this bug, you wonder?
Well, let’s assume they want to get their hands on a file with restricted access. Whether a password or file permission, unavailable due to security reasons, it would be stored on a DRAM memory cell. Their target is inaccessible, but they can force the cell that stores that information to flip by repeatedly flipping another memory cell that sits next to it.
Whether stealing data or frying your RAM in an unstoppable row hammering process, hackers could give you quite some headaches if they decide to pick up on the problem.
Since the DRAM rowhammer bug is a hardware flaw, there’s no patch for it. Manufacturers would have to make some adjustments in the process to correct this issue, an issue particularly sensitive in laptops and PCs where you can’t use ECC memory instead.
3.Blow your Network Interface Controller
This one is about malware that can corrupt your network equipment firmware. We talked before about how routers and modems get infected.
So, suppose you have even the slightest idea of the broader perspective of network infections. In that case, you know that most malware that targets networks and their equipment is either intended to spy on the traffic within the network or to use the network resources for DoS attacks.
DoS stands for Denial-of-Service and is an attack meant to flood a targeted machine or network with traffic or sending information towards the target that will trigger a crash.
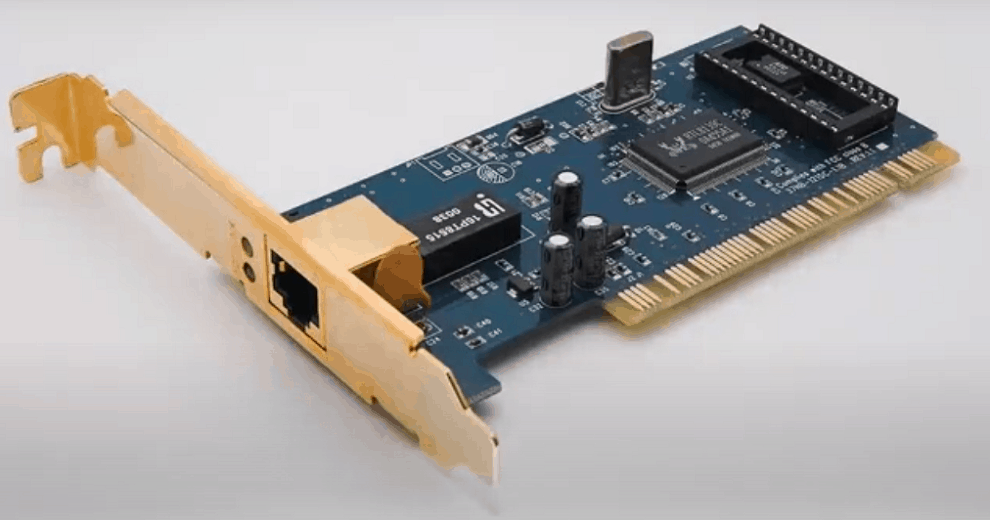
Viruses that blow your NIC
Now, when we talk about viruses that blow your NIC, we mean something even more serious, as in PDoS.
PDoS stands for Permanent Denial-of-Service. It’s a type of attack, not a virus per-se, and it is meant to allow a person to exploit network equipment firmware.
A PDoS attack could flash the firmware with malicious code. If the action leads to corrupt firmware, the targeted device will become inoperable. If the flashed firmware is programmed to do something evil, the hacker will gain control over the device, and the results will be hardly pleasant.
4.Make your hard drive permanently infected
Here, I’m not talking about malware that corrupts some files you store on your hard drive, and that will go away as soon as you format it.
I’m talking about malware that stays forever in computer hardware, that doesn’t go away, not even after you’ve installed a new, clean OS version.
More details on whether a factory reset removes malware, you’ll find here.
For now, I’m going to detail the “achievements” of Equation Group, a sophisticated cyber-espionage team that the security researchers from Kaspersky Lab identified back in 2015. As it turns out, those hackers have tapped into hard drive firmware reprogramming.
How is hard drive firmware reprogramming possible?
Whether it’s a traditional HDD or the newer SSD, any hard disk has several components. The most notable ones are the storage medium (magnetic disks for HDDs, flash memory chips for SSDs) and a microchip.
The microchip is this hardware part where software is embedded to include controls for reading and writing to the disk, along with multiple service procedures that help the hard drive detect and fix bugs.
You could call the hard drive’s microchip a small computer in itself because that’s what it is. It comes with its firmware, and this is the part that the hackers from Equation Group have managed to exploit.
By corrupting the firmware of the hard drive’s chip, they allow malware to read and write data on a particular subsection that can’t be touched even during disk formatting!

How does this make your hard drive useless?
With the new firmware version, the hard drive’s malware can reinfect the HDD/SSD’s boot area. Consequently, the moment you have finished reinstalling the operating system, the malware is back up.
The remarkable thing about firmware is that the firmware itself is in charge of checking its status (the integrity of its code) and running the available updates. As you can imagine, once the firmware was compromised at this level, it can no longer be trusted to eliminate its infection.
This is why infected firmware is indestructible and why most specialists agree that it’s easier and cheaper to throw away a compromised hard drive than to try and get rid of infected firmware.
Before you freak out, you should note, though, that the process itself of corrupting the hard drive firmware is exceptionally complicated. Because each hard drive model is unique and developing alternative firmware for it is time, resource, and money consuming, hackers have a tough time pulling this off. And they’re not interested in doing it to the regular user, either.
5.Prematurely wear your hard drive
Like any other piece of hardware, your hard drive comes with an expected life span. In time, as it writes, erases, and rewrites, it can physically degrade, and one day, you notice it cracked.
Nevertheless, there is yet another way you can come to this point, much faster than you’d want. That way is if a virus contributes to an existing action that can and will eventually break your hard drive.
That action is called disk thrashing, a loop where the hard drive keeps reading and writing information.
Now, disk-thrashing isn’t something that viruses and malware will deliberately cause to your device, BUT it is something they can aggravate. It has to do with how computers work.
How do computer and disk thrashing work?
Specifically, if your PC has insufficient RAM to run all the software you’re trying to keep active on it, it will rely on a virtual memory extension provided by the hard drive.
The moment that virtual memory extension from the hard drive becomes insufficient, too, disk thrashing hits the scene.
The way this occurs is if you have an older computer with limited system resources. Once it gets infected with viruses and malware, you may deal with disk-thrashing aggravation due to the malware infection.
As you can see, it’s a series of factors that will eventually make you buy a new hard drive, with the tip of the iceberg being touched by the virus infection.
6.Infect your PC motherboard
When it comes to viruses that attack hardware, any cybersecurity enthusiast will instantly think of the infamous Chernobyl virus. It was detected for the first time back in 1999. And its specialty was to corrupt data on hard drives and motherboard BIOS.
CIH (yet another code name of the Chernobyl virus) would brick any computer it would infect because it would overwrite the system information and destroy the BIOS in the process.
Still, we’ve come a long way since the late 1990s, and Unified Extensible Firmware Interface conquered the BIOS as we knew.
UEFI, a software interface between an OS and platform firmware, is the new kid on the block. This cool kid can do lots of things. UEFI allows you to reset a system’s or a platform’s firmware as opposed to the good old-fashioned BIOS that we couldn’t reflash.
Does UEFI make it all much safer?
So, in theory, modern computers don’t have the issue that the ones infected by the Chernobyl virus had. These days, it would require certain privileges for a virus to update the UEFI firmware with a modified, infected version.
UEFIs usually don’t accept updates that don’t carry their manufacturer’s digital signature, which makes their corruption seem less likely.
For a hacker to overwrite the UEFI on your motherboard with arbitrary code…
…he would have to have access to the mainboard manufacturer’s private key (which is typically held secret)
AND
…to spot an unintended security vulnerability of the UEFI that would allow overwriting the code.
So, it’s more challenging to make a motherboard unusable by breaking its UEFI. But…
(there’s always a BUT, isn’t it?)
It is also more likely to happen in the future because UEFI is becoming widespread, gaining more functionalities, and getting a larger attack surface. The more it develops, the higher the odds for hackers to spot hidden vulnerabilities.
7.Compromise USB-connected peripherals
Peripheral components used to get viruses through transferring infected files.
Thanks to the above-mentioned UEFI standard, however, we can now witness the corruption of a peripheral’s firmware, which can be further used to take the component out of service or gain control over it or the devices it connects to.
This isn’t recent news. It hasn’t been since July 2014, when security expert Karsten Nohl developed the so-called BadUSB exploit. His attack showed the world how any device that supports USB connectivity could become an infection vector.

What is the BadUSB exploit?
We are talking, once again, of malicious code that can work straight into the USB device’s controller chip. Corruption is possible because of a vulnerability in USB firmware, a vulnerability we can’t fix.
A BadUSB exploit allows a hacker to write or overwrite the firmware code of any USB device, reprogramming it to act and serve as a human interface device.
Once the attack is accomplished, the hacker can use it to run malicious software or execute commands on the computer to which you connect the infected USB device.
As long as the current USB operation standards remain in place, there’s no way to prevent such an attack.
The only thing one can do is to refrain from connecting any foreign peripheral to personal devices. Moreover, it wouldn’t hurt if you would disable any inactive USB ports and block automatic USB installations.
8.Compromise Thunderbolt-connected peripherals
This Intel-developed hardware interface that allows peripheral connections at lightning speeds compared to USB interfaces is not immune to vulnerabilities.
A Thunderbolt connection was proved to act as an infection vector for Mac devices. The villain was Thunderstrike, a bootkit designed explicitly for OS X devices. And if you know what a bootkit is, you have all the reasons to get the shivers just by thinking about this possibility.
Because infection through a hardware connection requires physical access to the device, experts coined the term “evil maid” attack, which also applies to infecting a device through a Thunderbolt connection.
Not so likely to get it, terrible once you do get it
The good news is that because Thunderstrike requires an evil maid attack, it is less likely to happen to you. It can only be transmitted through direct contact, which means you can get it on your device if the hacker literally gets his hands on it, or if you install it from a Thunderbolt-connected, already infected peripheral.
The destructive attribute of Thunderstrike, which earned it a place on this top of malware and viruses that affect hardware, is that you can’t get rid of it.
Once your device is infected with it, it remains permanently compromised. Reinstalling the OS won’t help because it is a bootkit that will launch itself the moment you turn on the device before the OS gets to boot.
With Thunderstrike in place, hackers get complete control of every process of the device. Whether you reinstall the OS or replace the SSD, Thunderstrike is there to remain on your MacBook.
9.Damage computer-controlled hardware
Last but not least, some viruses can damage computer-controlled hardware.

Imagine a factory where most processes are automated and overseed via computers. Suppose one of those computers is infected and it can no longer perform optimally. In that case, it will affect the functionality of the machinery it controls within the factory, thus causing hardware damage.
Remember Stuxnet, the virus we talked about in our ultimate list with computer virus names?
That one was meant to affect the centrifuges from an Iranian enrichment facility. It didn’t damage any computer hardware, but it damaged the centrifuges because it made the computers unable to signal a problem by disabling all system alerts.
Stuxnet wreaked hardware havoc by blocking the software safety measures in place. It is said that it damaged around 1000 centrifuges.
Without a doubt, it was a sophisticated virus and one that took enormous resources from its developers. The regular computer user will hardly become a target of such orchestrated attacks.
Still, it goes to show that wherever computers control hardware equipment, as long as there is an interest, there will be a way to tamper with it.