Having a rootkit on your computer makes you the most vulnerable. A hacker gains access to your system, and you have no idea what’s going on. The only way to change this unfair balance is to catch the threat as early as possible.
Can Antivirus detect rootkit? Antivirus can detect rootkit by recognizing malicious attempts of accessing system functions. Some software will run rootkit scans, looking for signatures. The best ones rely on behavioral analysis – they don’t search the actual rootkit, but rather rootkit-specific behaviors.
As always, the best antivirus software should catch a rootkit in progress and minimize the damage. If only you could avoid getting into such situations… But wait, you can stand a chance against rootkits! Follow the details below, and you’ll be much, much safer!
What is a rootkit?
A rootkit is a type of malware. Tricky to detect and remove, it can cause severe damage to any system.
Cybercriminals develop rootkits that stay hidden on the computers they infect, giving them remote access to those devices.
On the one hand, a hacker can see and access your online banking, credit card, or other important password information. On the other hand, it will use the rootkit to disable your Antivirus or make it ineffective and gain control of the operating system.
So, a rootkit is a malware that gives attackers remote control. It’s way more challenging to detect than most other malware types. It can go unnoticed for weeks or even months. And the extent of damage it can produce will very much depend on how you’re using the device through all that time.
What is the most dangerous type of rootkit?

Rootkits are shooting at the application level, system level, library level, or kernel level. Without a doubt, the kernel rootkit is the most dangerous type of rootkit. After all, it attacks the core of a system, and there’s nothing more dangerous than that.
To expand a bit on the topic, depending on where they install and what they compromise on a device, rootkits can be classified as:
- Hardware rootkit, which will infect the hard drive of a computer or even a router;
- Firmware rootkit, which will infect the BIOS;
- Bootloader rootkit, which will infect the bootloader, the one that is active before you turn on the operating system!
- Memory rootkit, which will target the RAM of your device and allow malicious activities in the background;
- Application rootkit, which will target standard files of applications such as Notepad, Word, Excel, or Paint, and give hackers access to your PC every time you run one of them;
- Kernel-mode rootkit: will infect the core of the operating system, giving hackers the ability to change the way the OS works.
As you can imagine, the least challenging of them all would be the memory rootkit. Because it activates in the RAM, it typically won’t last long. Rebooting the system is just about the end of its lifespan, although, in some instances, one might need extra steps to get rid of such a rootkit.
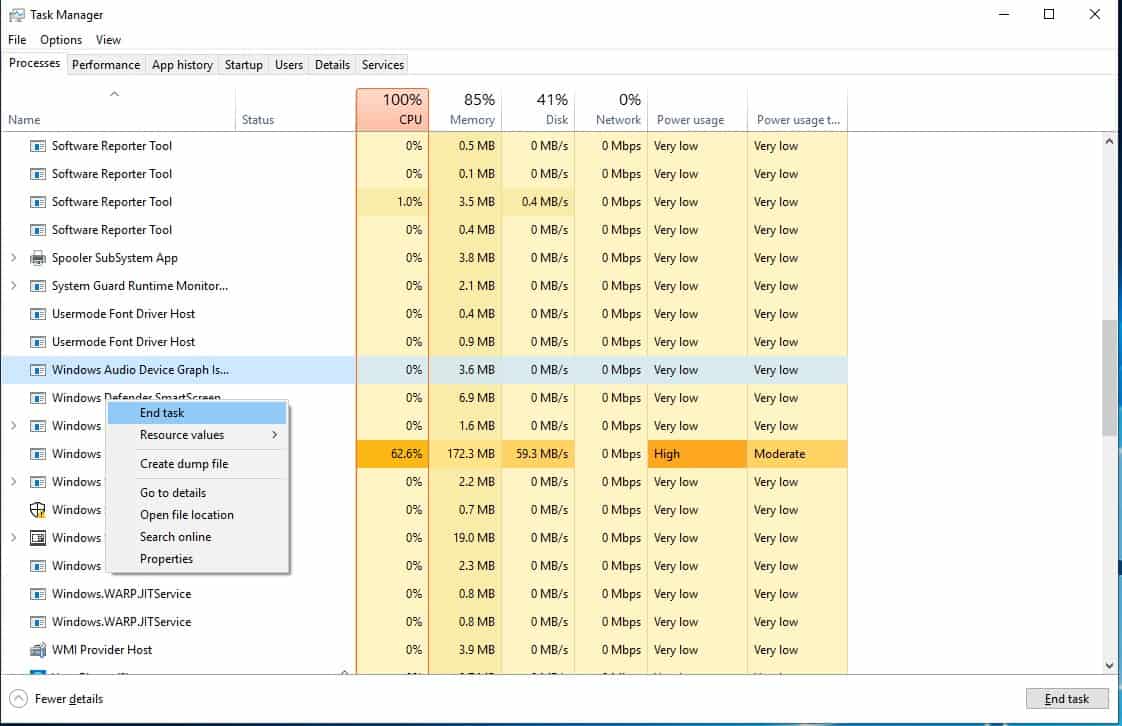
How do I know I have a rootkit?
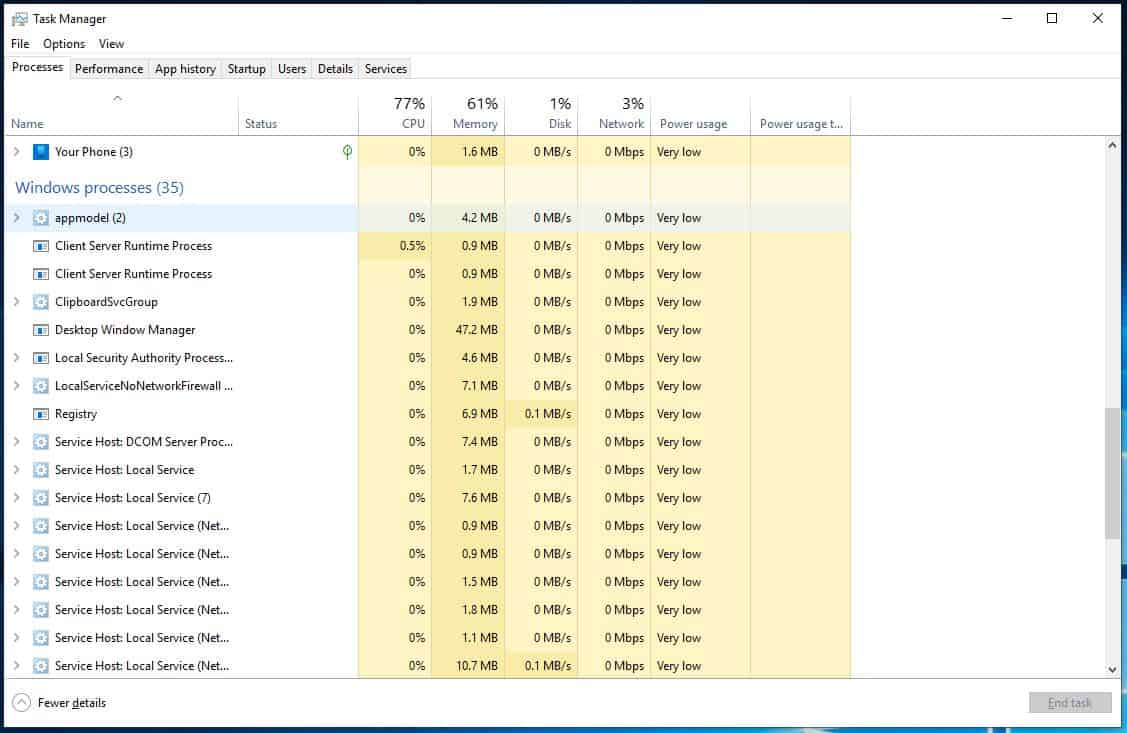
When a rootkit is active on your device, it communicates with the outside world. This translates into the existence of a running process. Not just any process, but one that responds to requests and relies on a port to maintain this communication.
The problem is that rootkits are more or less well hidden. And because they aim to stay like that, the signs of an infection are hardly eye-popping. You’ll have to know what and where to look for.
In theory, to know if you have a rootkit, you’d have to check the running processes and see if you spot anything that isn’t supposed to be there at the time. You could also try to scan your localhost in an attempt to find and open port.
In practice, however, you could do the two things from above and still not spot the rootkit – especially if it’s a well-hidden one. Because yes, well-hidden rootkits will hide from the process list. And those that rely on port-knocking will most likely not show up at a simple port scan.
That is why you might have to be proactive about it and run dedicated software, like advanced Antivirus that can detect rootkits.
Can Rootkits be removed?
Rootkits are just as hard to remove as they are to detect. In some instances, the only solution may be to wipe off the OS and reinstall it from scratch. If the damages aren’t beyond reparable, using a dedicated rootkit removal utility could do the trick.
Since more and more antivirus developers are beginning to develop rootkit detection methods, you should also have the option of removing one, using the same antivirus software that identified it in the first place.
One more thing to take into account is that some rootkits can be harder to remove than others. It depends on where they are embedded. The worst are the ones that target the firmware, like the BIOS firmware rootkits, for instance. Those are resistant even to the reinstallation of the OS!
How to prevent getting a rootkit

A rootkit can’t infect devices all by itself. It cannot spread itself without a transfer vehicle. And more often than not, it hides within functional software that you unknowingly choose to download, thinking it’s legitimate.
The moment you approve the software installation on your device, you’re also installing the rootkit along with that software. Even so, the rootkit won’t become active until the hacker chooses to activate it. So, it may lay dormant on your system for some time before the hacker decides to make use of it.
Now, compromised software isn’t the only way you can get a rootkit. Connecting to a shared drive from a compromised device is yet another common infection vector. The same goes for accessing shady websites and downloading something from there. Or you could get it from email phishing scams.
Knowing how rootkits work and how you can get infected should give you more specific clues on preventing getting a rootkit. But to provide you with some hands-on advice, here’s what you must particularly pay attention to:
Don’t download shady files
When someone you don’t know sends you something you haven’t asked for, beware! The temptation to download the file is big, but that’s the catch. Whether you’re curious to download a file, or to open an attachment, or to click on a questionable link, please don’t do it. Better to be safe than sorry!
Protect yourself from drive-by downloads
Drive-by downloads are particularly dangerous because many internet users don’t realize the dangers. You can get malware – or, in this case, a rootkit – by merely accessing an infected website. You don’t need to download anything while in there. The installation is automatic.
What’s worse, drive-by downloads can occur even on legitimate websites that were hacked for this purpose. So, a website that doesn’t look suspicious at all can have malicious code embedded in it. Because you cannot spot this danger all by yourself, focus on protection against drive-by downloads:
- Keep all your software up to date to enjoy the latest security patches;
- Consider installing some dedicated web-filtering software, which may prevent you from accessing compromised websites;
- Use your computer from a user account, not an admin account.
Don’t take the bait of phishing emails

Phishing emails typically lure you into clicking on a link. This can either result in downloading something – like… a rootkit – or redirect you to a compromised website where you can – see the point above – get a drive-by download.
The reason why so many people still fall for these phishing emails is that they can be compelling. They try to emulate communication from a financial institution, like a credit card provider or bank. It’s understandable if you want to address whatever message you have from a financial institution. But you should never do it from a link sent from an email.
Instead, whenever you’re asked to verify your identity or to update some information, use a separate tab in your web browser and manually type the URL of that institution’s website. Do the login manually rather than following a link from an email!
Never ignore an update notification
Whether it’s for the antivirus software, for the operating system, or for particular applications, the moment you get notified about an update, take it. Updates are meant to improve both the performances and the security of the software they address.
By running the latest software versions, you enjoy the highest level of protection. It’s the least you can do while fighting this sneaky type of malware known as a rootkit.